The Microsoft store is a useful app, but realistically, no-one needs it pinned to the taskbar, especially on Intune managed machines where you want everyone using Company Portal.
So, how do we remove it? In this post I’m going to run through the 4 different options available to you:
- Registry
- PowerShell Script
- Proactive Remediation
- Custom OMA-URI
- ADMX Importing
- ADMX Ingestion
I should warn you now, two of them simply don’t work!
Registry
The easiest one to start with, if you look at old fashioned GPO, there is a policy called NoPinningStoreToTaskBar which removes and blocks it from being re-added.
If we visit the ever useful admx.help website here we can see the exact registry key it is applying
Using whatever tool you prefer, simply apply this key:
Windows Registry Editor Version 5.00
[HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\Explorer]
"NoPinningStoreToTaskbar"=dword:00000001This isn’t my preferred way though because it needs a reboot and it just feels a bit clunky
PowerShell Script
Now we’re more into my territory! We can deploy a PowerShell script in the user context to find the app and unpin it (script here)
$apps = ((New-Object -Com Shell.Application).NameSpace('shell:::{4234d49b-0245-4df3-b780-3893943456e1}').Items())
foreach ($app in $apps) {
$appname = $app.Name
if ($appname -like "*store*") {
$finalname = $app.Name
}
}
((New-Object -Com Shell.Application).NameSpace('shell:::{4234d49b-0245-4df3-b780-3893943456e1}').Items() | ?{$_.Name -eq $finalname}).Verbs() | ?{$_.Name.replace('&','') -match 'Unpin from taskbar'} | %{$_.DoIt(); $exec = $true}As you can see, it’s looking through the taskbar for any apps which contain Store, then grabbing the name and calling an Unpin
It’s quick, it’s easy and it works. But, it only runs once…
Proactive Remediations
Enter my favourite, Proactive Remediations, let’s take the code which works and feed it into a Proactive Remediation, it will give us better control, more reporting and we can set it to repeat for any naughty users
First up, we need to detect it (script here)
##We're looping through the verbs so it's going to be easier to count
$pinned = 0
##Loop through verbs for the store app
$apps = ((New-Object -Com Shell.Application).NameSpace('shell:::{4234d49b-0245-4df3-b780-3893943456e1}').Items() | Where-Object { $_.Name -eq "Microsoft Store" }).verbs()
foreach ($app in $apps) {
##Is Unpin an option?
if ($app.Name -eq "Unpin from tas&kbar") {
##Yep, increment the counter
$pinned++
}
}
#Has it been found?
if ($pinned -gt 0) {
Write-Warning "Store has been pinned"
exit 1
}
else {
write-host "Not pinned"
exit 0
}This time, we’re looking for any apps with store in the name and then simply checking if we found any. If we did, send an exit 0 and remediate:
Remediation script here
$apps = ((New-Object -Com Shell.Application).NameSpace('shell:::{4234d49b-0245-4df3-b780-3893943456e1}').Items())
foreach ($app in $apps) {
$appname = $app.Name
if ($appname -like "*store*") {
$finalname = $app.Name
}
}
((New-Object -Com Shell.Application).NameSpace('shell:::{4234d49b-0245-4df3-b780-3893943456e1}').Items() | ?{$_.Name -eq $finalname}).Verbs() | ?{$_.Name.replace('&','') -match 'Unpin from taskbar'} | %{$_.DoIt(); $exec = $true}Exactly the same as the standard PowerShell script
Custom OMA-URI
After digging through the Microsoft documents, I found the CSP here
Which would give me this URI:
./User/Vendor/MSFT/Policy/Config/ADMX_Taskbar/NoPinningStoreToTaskbarAfter deploying the policy with a setting of 1 it immediately failed with a generic error 0x87d1fde8, so off to the Event Logs (Applications and Services – Microsoft – Windows – DeviceManagement-Enterprise-Diagnostics-Provider – Admin.
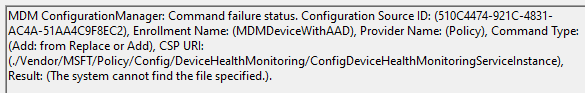
Checking the registry confirms it isn’t there:
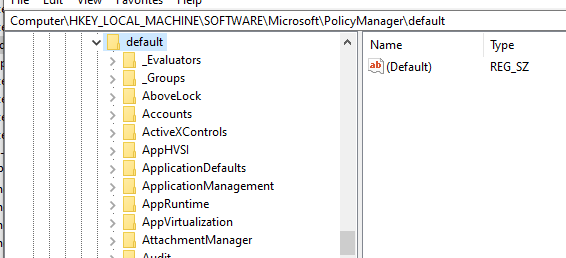
Clearly this policy isn’t yet supported out of the box (which is probably why it’s not in Settings Catalog)
Let’s try something else
ADMX Importing
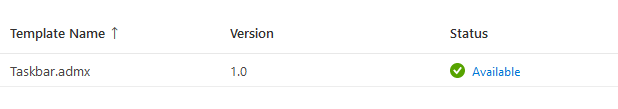
Using the new Preview feature to import ADMX files, I grabbed the Taskbar ADMX and ADML files from my domain controller and imported them in
Upload and Import successful, looking positive
So onto a policy:
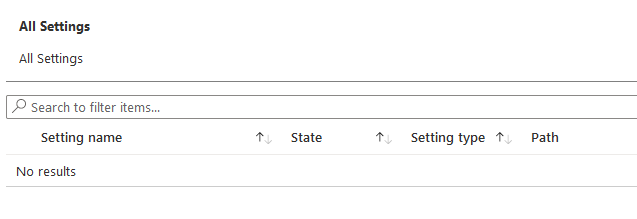
Safe to say that’s not going to work either. One more thing to try
ADMX Ingestion
The old fashioned approach, first I took the Taskbar.admx policy and stripped out everything I didn’t need, leaving this:
<?xml version="1.0" encoding="utf-8"?>
<!-- (c) 2006 Microsoft Corporation -->
<policyDefinitions xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" revision="1.0" schemaVersion="1.0" xmlns="http://schemas.microsoft.com/GroupPolicy/2006/07/PolicyDefinitions">
<policyNamespaces>
<target prefix="taskbar" namespace="Microsoft.Policies.TaskBar2" />
<using prefix="windows" namespace="Microsoft.Policies.Windows" />
</policyNamespaces>
<resources minRequiredRevision="1.0" />
<policies>
<policy name="NoPinningStoreToTaskbar" class="User" displayName="$(string.NoPinningStoreToTaskbar)" explainText="$(string.NoPinningStoreToTaskbar_Help)" key="Software\Policies\Microsoft\Windows\Explorer" valueName="NoPinningStoreToTaskbar">
<parentCategory ref="windows:StartMenu" />
<supportedOn ref="windows:SUPPORTED_Windows_6_3" />
<enabledValue>
<decimal value="1" />
</enabledValue>
<disabledValue>
<decimal value="0" />
</disabledValue>
</policy>
</policies>
</policyDefinitions>Then I created a quick policy to Ingest the ADMX template into here:
./Device/Vendor/MSFT/Policy/ConfigOperations/ADMXInstall/MSStore/Policy/TaskbarADMXAgain, another error in Intune, back to the event logs and we have a new error:
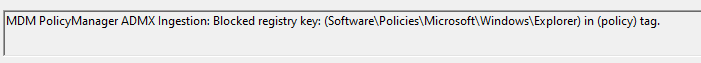
Digging around further on Microsoft Docs and I found this page, in particular this part:
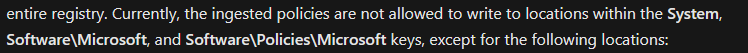
As we saw in the original registry key, that’s exactly where it populates!
Conclusion
So, the end result is, until the ADMX policy is allowed, or added to Settings Catalog, PowerShell is basically your only option for dealing with this!

you can configure this now using the Intune settings catalog Policy or csp
Go to the Intune portal and navigate to Devices > Windows.
Select Configuration profiles and click Create profile.
Choose Settings Catalog.
Provide a name and description for your profile.
Add a setting and search for “Do not allow pinning Store app to the Taskbar (User)”.
Enable the setting and choose whether to apply it to all users or specific user groups.
Click Next to review and then Create to deploy the profile.
Thank you, definitely the easier option!
For those looking for the Intune setting it resides in the Settings Catalog under Administrative Template as
“Show Windows Store apps on the taskbar (User)”
Thank you!
@maurice v Boxtel
Hi
The admin template that you mentioned is not working, did you add any other changes?
As far I can tell it is now possible to have te store unpinned from the taskbar within a template in Intune:
StartMenu & Taskbar
Show Windows Store apps on the taskbar (User) Enabled/Disabled
If you roll this out to a device group it will remove the store icon from the taskbar.
That’s a very welcome update, thanks for pointing it out
Hi Andrew,
Working with a local language version like me (Danish) I had to look for the Danish word for “unpin from taskbar” 🙂
Do you know of any way to look for this in all languages in one script.
Can we find the verbs in English on a Danish version of win11?
I could make multiple lines to remove the icon (one for each language), but it owuld be nice not ta have to do this. 🙂
Hi,
As far as I can see, it’s per language, are there any words the same?
The other option is build an array in every possible language and then check if the verb is in the array so would only need one script instead of multiple
Only from the pinned apps.
If you push out a custom start menu layout, that removes all default pinned apps.
Have a look at this post
Do you have a solution for unpinning the Store from start, all scripts I found did not Work.
From just the pinned apps, or from the menu completely?